Business has been moving to the cloud since before the coronavirus pandemic, and this trend has been accelerating these past few years. Meanwhile, workplaces are diversifying, the dividing line between work and home has been getting less distinct, and cyber attacks targeting that in-between space are on the rise. In this document, we talk about SASE and ZTNA, which are gaining even more attention as security measures amidst the COVID pandemic.
1. What is SASE?

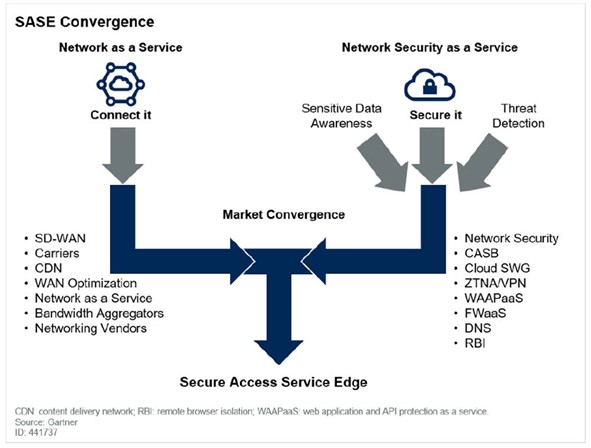
“SASE” stands for “Secure Access Service Edge”, a cloud-based network security model that Gartner proposed in 2019. This combines both the network system and the security measures, so that installing SASE allows the user to manage both the network and network security together.
The business environment prior to the spread of the cloud mostly involved work concluding entirely within the corporate network, and while there was occasional remote access via a VPN, this was generally restricted, such as to specific departments or types of work.
That said, in recent years, the spread of COVID has prompted a rapid increase in remote work and a real diversification of the work environment. It has also become common for employees to connect to a company’s systems via a VPN from home or from a coworking space, and use services provided in the cloud to carry out their work.
Workplace and data asset locations have diversified, making it more difficult for a company’s IT department to manage everything under a unified security policy.
SASE brings network services and security services together, making it possible to maintain security without getting in the way of employee work, while also reducing the burden on system administrators.
2. What is ZTNA? How this relates with SASE
“ZTNA” stands for “Zero-Trust Network Access”, and offers solutions and features to control user access at the application level in ways that do not involve having to trust the users at all.
“Zero-trust” treats all communication as potentially suspect, regardless of whether it originates from within or from outside of the company. This approach is gaining more interest in recent years, as the borders between “inside” and “outside” have blurred.
ZTNA controls access at the application level by evaluating the user upon each instance of communication, making it possible to carry out work safely and securely, in a remote environment or on-site, without regard to where communications originate.
ZTNA is one part of what makes up SASE. SASE also includes security solutions like CASB and SWG, and network solutions like SD-WAN and CDN, which we will talk about later.
Related article: What is ZTNA?
3. Why SASE is necessary

Let's take a fresh look at the background leading up to how SASE has become important.
1) Accelerating shift to the cloud
The COVID pandemic has sped up the shift towards remote work and working in the cloud, with more and more companies implementing Microsoft 365, Box, and other cloud services in their workflows. When working in the cloud, users do not need to choose where they work, making cloud-based approaches well-matched to the working styles of today’s businesspeople.
Meanwhile, the rapid rise in use of the cloud and remote work means that employees have encountered a corresponding rise in network lag and other problems affecting their remote access.
2) Limits of the conventional border-based security model
Security efforts in the past have been based on borders, functioning to delineate a clear boundary between the “inside” of the company network, and the “outside”. The rapid adoption of remote work has meant that the border between this “inside” and “outside” has gotten very fuzzy.
It has become vital for people to have a network environment in place that facilitates safe and easy work in any location, and VPN and other border-based security models of the past are struggling to keep up with modern needs.
3) Growing burden for system administrators
Companies have more options for where to put their information assets, such as on-premises, private cloud, or public cloud solutions. The situation might even be called chaotic for some companies.
Employees are now trying to access these information assets from any location, and from any device. This has led to spiraling growth in the burden for the system administrators who must configure the security policies for each server, network, and device. Software isn’t the only issue, as a growing user base also means a growing number of hardware devices that must also be managed—further increasing complexity.
4. The advantages of implementing SASE
Implementing SASE provides a single solution for all of these issues.
1) Unified cloud and security management
The SASE solution integrates network and security features, allowing for unified management of both the cloud and security. Administrators can manage access to information assets safely, regardless of whether users are “inside” or “outside”, by configuring standard security policies via dashboards and other tools.
2) Increased security, without inconveniencing employees
When users are working remotely, SASE with ZTNA can directly connect applications and user devices without needing to go via internal company systems. This reduces the chance of network lag from increased traffic and makes it possible to increase security without causing any employees to lose their work.
3) Reducing the overhead of system operations management
Introducing SASE can reduce the amount of system administrator work: this allows you to manage security policies and logs via a unified and standardized platform, and by reducing the number of network devices that require management, you are freed from the complicated task of scaling out your own on-premises servers and network devices otherwise needed to support remote work.
5. Sample of the features included in SASE

SASE includes various features and solutions. The current state of the market is that each vendor offers its own different feature set, so here we introduce a typical example.
1) ZTNA
Let’s look at ZTNA first. This improves security at the time of remote connection by handling user authentication and authorization for each application separately. ZTNA communication happens via a vendor access point. This can limit the company’s attack surface, as well as the potential for network lag.
2) SWG
“SWG” stands for “secure web gateway”, a security solution provided in the cloud, that includes features such as URL filtering, antivirus, and sandboxing.
3) CASB
“CASB” stands for “cloud access security broker”, a means of visualizing the current state of use and detecting any threats for cloud services. This visualization helps in setting standardized security policies for employee use of the cloud, and helps in detecting any unauthorized access from outside or inside.
4) SD-WAN
“SD-WAN” stands for “software-defined wide-area network”, a kind of virtual WAN. This enables remote configuration and central control of networks, reducing the system administrator’s workload while also allowing for safe use of the network.
5) Firewall
A firewall protects a company’s network from unauthorized access and other attacks coming over the internet. Firewall capabilities have been improving over the years with improved protection against threats and intrusions, and they can help defend a company against advanced malware attacks and even respond to targeted attacks.
6. Is SASE really necessary?
We’ve given you an overview of what SASE is. SASE includes various features such as ZTNA and CDN, but currently there is no single comprehensive solution that covers all of the bases.
For example, the SASE solutions currently in use around the world do not all include ZTNA functionality. Should a company try to replace their entire existing network infrastructure with an SASE implementation, they would often have to completely revise their current network configuration. Implementation and migration would thus likely take a considerable amount of time and resources.
We think any choice of product would have to be after carefully evaluating which security features are most needed. "Safous” is a ZTNA product to complement an SASE implementation, by safely connecting remote users to approved assets in an organization’s network, cloud, or IoT environment. Please give Safous a try and experience its ease of use.
Receive the latest news, events, webcasts and special offers!
Share this
You May Also Like
These Related Stories
%20Featured%20image_%20Blog_%20How%20is%20ZTNA%20different%20from%20VPN_%20(1).png)
Blog: How is ZTNA different from VPN?
%20Featured%20image_%20Blog%20Zero%20Trust%20vs.%20Legacy%20Security%20Systems_%20What%E2%80%99s%20the%20Right%20Choice_-1.png)
Blog: Zero Trust vs. Legacy Security Systems: What’s the Right Choice?

